Everyone having a website knows about the benefits of having a HTTPS enabled website. And the recent changes in modern browsers warning users about non-HTTPS sites makes the need of getting a certificate for website even more urgent. And certificates for making it happen are often a costly affair - ranging from a few bucks to thousands. But there are solutions that allow doing this for free. Each one has its own purpose, limitations and benefits.
The most simple option is to go for CloudFlare SSL, it will allow you not only to get HTTPS for your website but also speed up your website by serving the content to user via the nearest server. Also, it will hide original address of your web server. But it has its own limitations, like if your traffic exceeds certain limit, you will have to upgrade. And because you already pay for your hosting (assuming you do not host it on free hosting options like Google Drive, GitHub Pages, Surge etc), it would be wise to save a few bucks when you are only starting your blog.
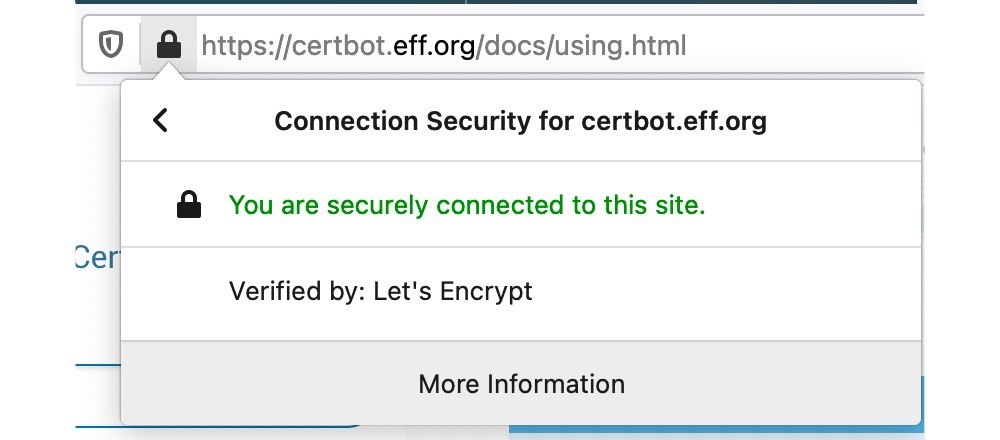
In this article, we will discuss about getting SSL certificates from LetsEncrypt (sponsored by EFF, Mozilla, Google and a lot of other companies).
LetsEncrypt supports certificates for any number of websites, sub-domains (including hosted on private IPs) and even wildcard certificates - all for free. It has only one limitation - the certificates expire in 90 days. And based on best practices, you should renew your certificate at least 30 days before expiry of your certificate. So, it means you have to renew (for free) your certificates every two months.
Usually many hosting providers support generation of LE Certificates, but some do not like NameCheap. Here we will explore the ways to get a certificate for deployment at a server of your choice using your local machine. All you need is access to terminal/ command prompt to run the programs to request and generate a new certificate.
There are many clients which offer GUI for generating certificates, but lack the verbosity of the terminal. And some end up giving you PFX format which you need to convert to PEM format before using. Here, we will go the terminal way.
LetsEncrypt issues two kinds of certificate: Wildcard domain certificate and a simple certificate.
The setup differs little for both of these certificates, like a simple certificate requires HTTP based file authentication and a wildcard certificate requires a TXT record/DNS based authentication.
Here, it is assumed that you do not have shell access and the instructions are made for using the Certbot ACME client in manual mode (obtaining certificate on a machine other than the target webserver). So, let's begin!
Also, note that you can request certificates for subdomains hosted using private IPs (for internal websites). But it will require DNS based authentication, as the FQDN would point to private IP at the time of requesting the certificate. And since, LetsEncrypt needs a way to authenticate the user for ownership of the given (sub-)domain, DNS is the only way to prove it. So, for such sub/domains, you will need to choose the preferred challenge as dns, and proceed.
The first thing you would need is access to terminal. Then you will need to install OpenSSL and Certbot.
After both tools are installed, you can run:
sudo certbot certonly --manual --preferred-challenges http -d example.comNow, the above line of code asks the certbot client to issue a certificate for example.com website (you can add www support by adding -d www.example.com at the end of above command) with http challenge i.e. you will have to place a file in your .well-known/ directory of root of selected website (for each -d option).
After entering this command, you will be asked for a valid email address for registering an account with the ACME server and agree to terms of service (if you have not done that already).
Note: You can skip email address for getting a certificate using --register-unsafely-without-email option, but you will then be unable to receive notice about impending expiration or revocation of your certificates or problems with your Certbot installation that will lead to failure to renew.
You may be asked to sign up for receiving email newsletters from EFF.
After sign up is complete (a one time process for each machine), the certbot will try to perform the challenges. As the command above has chosen manual mode, you will be asked to place files to specified path accessible over HTTP for each -d (sub)domain.
Example of http challenge output:
Performing the following challenges:
http-01 challenge for example.com
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Create a file containing just this data:
5CkcbzxO31IFArA16goT3hyp2eXutZIEDB8OqbAEBQU.n0nrpb4DdQhS6dsnVeahaIGsf60shEbTP_TiKPigINo
And make it available on your web server at this URL:
http://example.com/.well-known/acme-challenge/5CkcbzxO31IFArA16goT3hyp2eXutZIEDB8OqbAEBQU
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Press Enter to ContinueYou will have to perform above task for all -d options. And you will need to keep the files until all such (sub)domains have been verified:
(This must be set up in addition to the previous challenges; do not remove, replace, or undo the previous challenge tasks yet.)After completion of http challenges, you will see similar output:
Waiting for verification...
Cleaning up challenges
IMPORTANT NOTES:
- Congratulations! Your certificate and chain have been saved at:
/etc/letsencrypt/live/example.com/fullchain.pem
Your key file has been saved at:
/etc/letsencrypt/live/example.com/privkey.pem
Your certificate will expire on 2021-06-05. To obtain a new or tweaked version of this certificate in the future, simply run certbot again. To non-interactively renew *all* of your certificates, run "certbot renew"
- If you like Certbot, please consider supporting our work by:
Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate
Donating to EFF: https://eff.org/donate-leCongrats on getting your SSL certificate for free. These can be accessed at the path specified in the output. In my case, it was /etc/letsencrypt/live/example.com/. But, you might not be able to access this directory for obvious security reasons.
So, to access those, you need to set the permissions to 755 for both private key and directories containing it (/etc/letsencrypt/live/ and /etc/letsencrypt/archive/):
sudo chmod 755 /etc/letsencrypt/live
sudo chmod 755 /etc/letsencrypt/archive
sudo chmod 755 /etc/letsencrypt/live/example.com/privkey.pem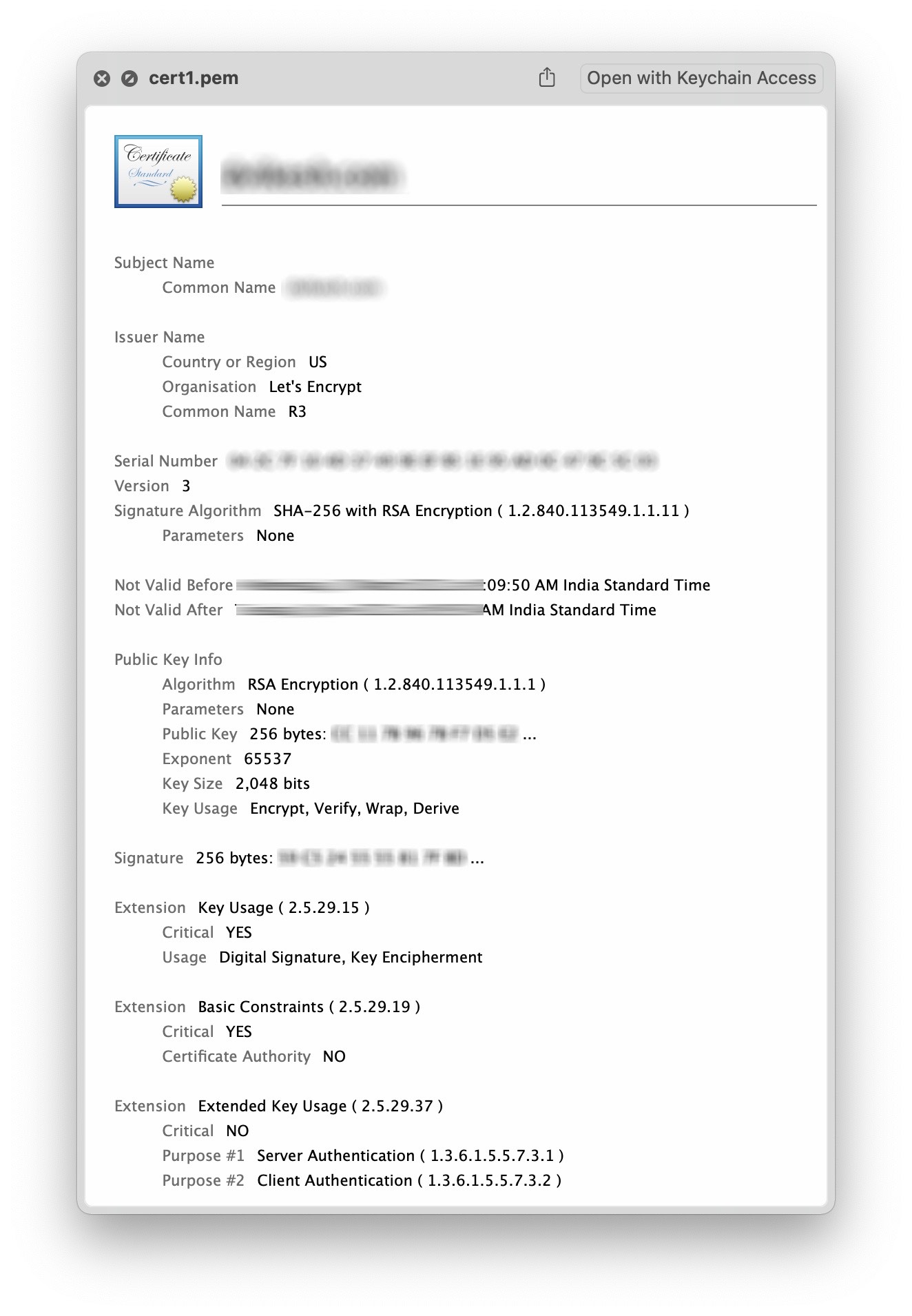
After deploying these certificates to server, you can delete the files that the challenge asked you to place (you may keep them for easier renewal though). And it will be a good advice to restrict the access to the private key and certificate directories as well:
sudo chmod 700 /etc/letsencrypt/live/example.com/privkey.pem
sudo chmod 700 /etc/letsencrypt/live
sudo chmod 755 /etc/letsencrypt/archiveAnd in case, your private key gets compromised, you can always revoke it using the following command:
sudo certbot revoke --cert-path /etc/letsencrypt/live/example.com/cert.pemYou may note that here the revoke command takes the certificate as its input. And you may specify a reason as well like --reason keycompromise. After revocation, the domain may be removed from the system to avoid accidental renewal:
sudo certbot delete --cert-name example.comYou might also get a renewal reminder from LetsEncrypt for renewal of your certificate 30 days prior to its expiry on your registered email.